
Knowledge Base
Microsoft sunsetting support for Cross-Signed Root Certificates with Kernel-Mode Signing capabilities
Description
On August 1, 2019, Microsoft announced the Microsoft Trusted Root Program is ending support for cross-signed root certificates with kernel-mode signing capabilities. In 2021, most of the cross-signed certificates expire.
In order to have your signature be compliant with Microsoft Guidelines, it will need to expire prior to June 30, 2021. You can use the custom_expiration_date API variable to create a copy of your certificate with an appended expiration date. If you have any additional questions, please contact our support team.
When the cross-signed certificate that your code signing certificate is chained to expires, you will no longer be able to create new kernel-mode digital signatures. This affects all version of Windows. To learn more about Microsoft's deprecation plans for kernel-mode digital signatures, see Deprecation of Software Publisher Certificates, Commercial Release Certificates, and Commercial Test Certificates.
Note: All existing cross-signed root certificates with kernel-mode signing capabilities continue to work until they expire. See Expiration dates of DigiCert brand trusted cross-signed certificates.
Microsoft's new process for driver submissions
Starting in 2021, Microsoft will be the sole provider of production kernel-mode code signatures. Microsoft has implemented a new process for signing kernel-mode driver packages. You will need to sign any new kernel-mode driver packages by following Microsoft's updated Hardware Submission instructions. See Partner Center for Windows Hardware.
What is DigiCert doing about this?
As a first step in this sunsetting process, DigiCert has removed the Microsoft Kernel-Mode Code platform option from Code Signing certificate request forms: new, reissue, and renew.
This means going forward, you can no longer order, reissue, or renew a code signing certificate for the kernel-mode platform.
How does this affect my existing kernel-mode code signing certificate?
If your code signing certificate expires after June 30, 2021, you can no longer use it to sign kernel-mode code, effective immediately. Contact Digicert to obtain a new certificate that expires earlier. If your certificate expires before June 30, 2021, you can continue to use your code signing certificate as follows:
- To sign non-driver code until it expires.
- To sign kernel-mode driver packages until the cross-signed certificate it's chained to expires.*
If you need to sign new kernel-mode code driver packages after the cross-signed certificate it's chained to expires, you need to follow Microsoft's updated Hardware Submission instructions. See Partner Center for Windows Hardware.
How does this affect my kernel-mode driver package signatures?
- If you sign and timestamp the kernel-mode code driver package before the cross-signed certificate it's chained to expires, your signature will continue to work after the cross-signed certificate expires!
- If you only sign the kernel-mode code driver package before the cross-signed certificate it's chained to expires, your signature will become invalid when the cross-signed certificate it's chained to expires.
For information about when the DigiCert branded cross-signed certificates expire, see the Expiration dates of DigiCert brand trusted cross-signed certificates section below.
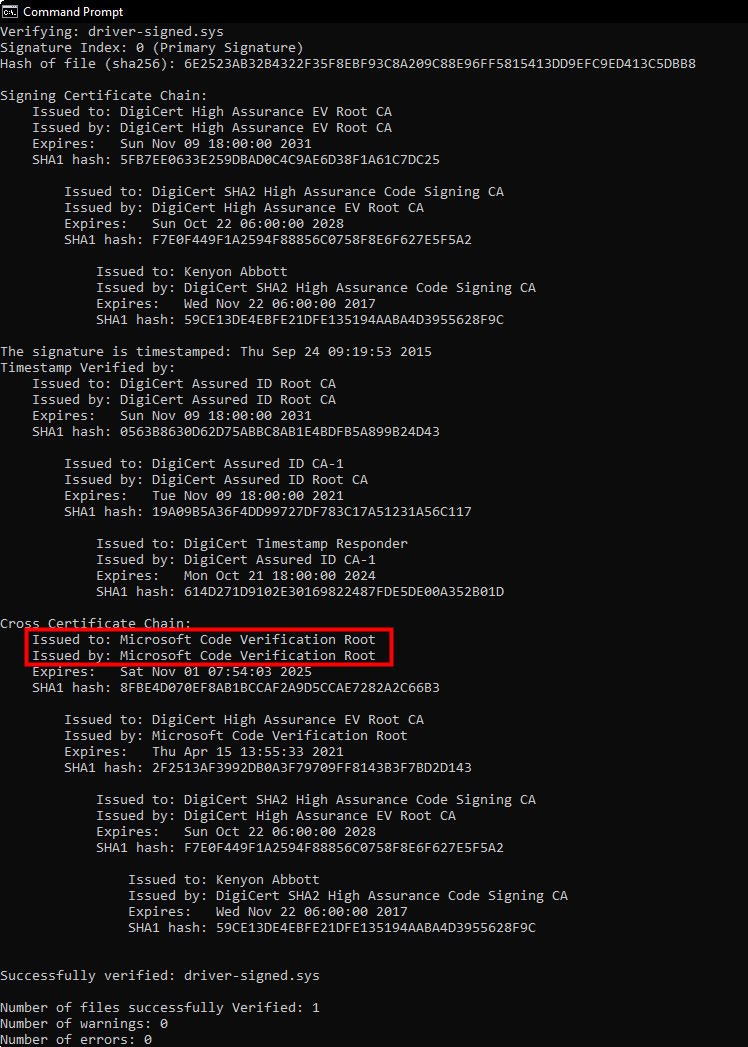
How do I know if my drive packages will be affected by a cross-signed certificate expiring?
If your certificate chain ends in Microsoft Code Verification Root, your drive package is affected.
To view the cross-signed certificate chain, run signtool verify /v /kp <mydriver.sys>
For example:
Expiration dates of DigiCert brand trusted cross-signed root certificates
- DigiCert Assured ID Root CA -- Expires 4/15/2021
- DigiCert High Assurance EV Root CA -- Expires 4/15/2021
- DigiCert Global Root CA -- Expires 4/15/2021
- GeoTrust Primary Certification Authority -- Expires 2/22/2021
- GeoTrust Primary Certification Authority - G3 -- Expires 2/22/2021
- Thawte Primary Root CA -- Expires 2/22/2021
- Thawte Primary Root CA - G3 -- Expires 2/22/2021
- VeriSign Class 3 Public Primary Certification Authority - G5 -- Expires 2/22/2021
- VeriSign Universal Root Certification Authority -- Expires 2/22/2021

